magnet™
Module overview
In its basic function, magnet allows the administration of all master data such as accounts, counterparties, users and much more. It thus forms the foundation for all other magnet™ modules and also allows the exchange of data between the different modules. In addition, magnet also contains the configuration of the security-relevant settings, which are explained in more detail in the section below.
Liquidity Planning
- Scenario Manager
- FX-Exposure
- Hedge-Ratio
- FX-Hedging
- Rate simulations
- Deviation analyses (is, plan)
Netting
- Multilateral Netting
- Service-/Profitcenter
- Payable/Receivable
- EFT-Processing
- IC-Bookings
Financial Accounting - Interface
- Creation of debtor payment files
- Posting batch
- Posting file
- Different reports
RPA (Robotic Process Automation)
The magnet agent is responsible for enabling automatic exchanges between client servers and magnet. By implementing RPA technology, companies can streamline their processes and make them more efficient by automating repetitive, manual tasks.
The agent monitors drive directories and uploads very fast bulk payment files, OP lists and Excel files etc. to magnet™ after saving.
In addition to the high level of automation, in particular the security aspect takes on a high importance – manipulation of payment files, for example, can be practically eliminated.
Price
Like our software, the usage fees are modular. Therefore, they are calculated individually for each configuration. In addition to these monthly usage fees for licence costs, server rental, maintenance/updates, the estimated one-off implementation costs are also adapted to the customer and their magnet™ configuration.
We invite you to fill out the price request form. We will then send you an individualised rough offer as soon as possible.
If you are unsure which modules and e.g. the number of users you need, we recommend a presentation of our software in advance. On the occasion of this product presentation, we will address your individual needs. You will then receive a price quotation based on your needs.
Contact us today to arrange a presentation appointment.
Security and Compliance
Compliance is essentially about separation of functions and process monitoring. There are legal requirements for due diligence. Among other things, a company must know its financial and asset situation at all times. Separation of functions means that whoever trades is not allowed to process, book and value these transactions. And of course the other way round.
The security-critical processes in magnet™ meet the highest standards and are divided into three areas:
User management:
This includes, for example, role-based authorisations per company as well as a signature regulation with amount limits.
4-eyes principle:
All changes in the system administration and user administration of magnet™ are subject to the “4-eyes principle”.
System administration:
This is where the security-critical processes are defined, e.g.:
- Policies for payment transactions
- Security Policy and everything regarding passwords (e.g. how structures, length, validity, etc.).
- Two-factor authentication with codes for login procedures, signatures and payees
- IP restrictions
Technical information
Modern applications are based on a “Service Oriented Architecture” (SOA). SOA is neither a product nor a technology standard, but a technology-independent concept for the architecture of software systems. magnet™ is based on SOA. But what is the benefit of SOA? The functions of a software should be available as independent building blocks with clearly defined functional tasks, web services, and only loosely coupled with each other. This makes it possible to change individual services or the relationships between services without having to rework the whole system. It’s also one of the requirements for cloud operation. And this is also one of the reasons why softcash ag can offer both cloud and on-premise solutions.
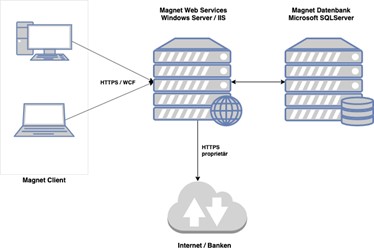
magnet™ is a classic client/server application. The client is a Windows Forms application that is distributed via the ClickOnce deployment model of the .Net framework. Therefore, no installation is necessary on the Windows client machine. The application is downloaded via the web and executed in the .Net Framework sandbox. The communication between client & server is based on WCF (Windows Communication Framework) via the default https port 443. The browser must support ClickOnce Prefix. This is the case by default for all versions of Windows Internet Explorer and Windows Edge. Add-ons are available for Firefox and Google Chrome.
Software documentation
Of course, the most comprehensive product descriptions are no replacement for getting to know magnet™ in a live version. The following documentation (available for download as a PDF document) will at least give you a brief first impression.